Introduction
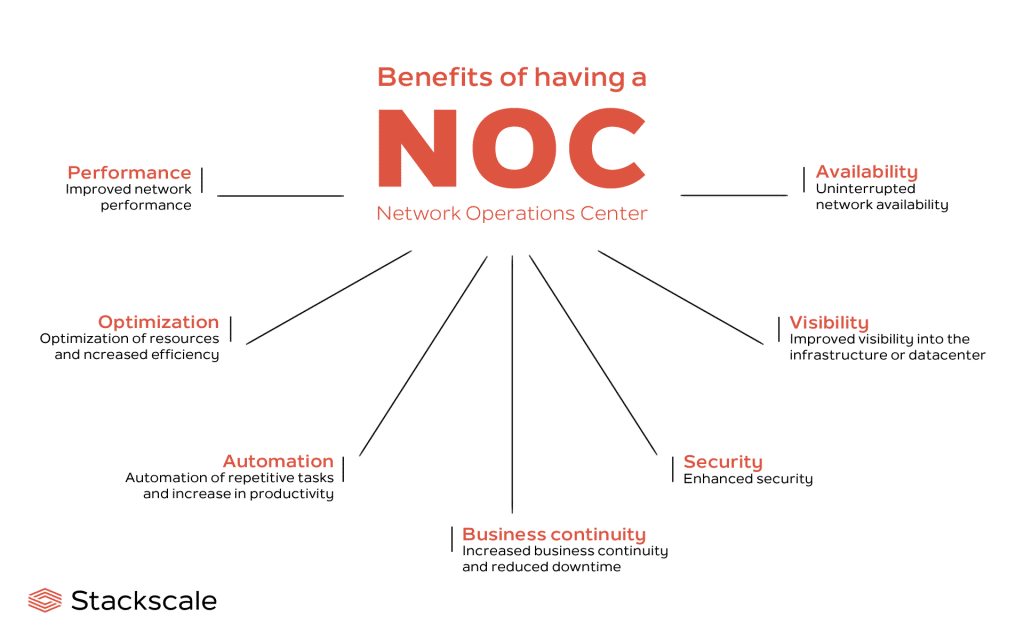
Maintaining network performance, reliability, and security has become critical to a business of any size. Furthermore, as organizations become increasingly reliant on interconnected systems and service delivery, a Network Operations Center (NOC) becomes essential in network health maintenance. For many businesses, leveraging managed NOC services ensures that these operations are handled efficiently and with expert oversight.
A NOC is tasked with observing, controlling, and resolving issues concerning a network’s infrastructure. However, the network monitoring reporting quality is directly proportional to the coverage and detail of the monitoring done. With the support of managed NOC services, the monitoring gap can determine whether a network operates seamlessly or incessantly suffers disruptions.
In this blog, we’ll discuss the key network monitoring services that every NOC should provide to maintain infrastructure security, efficiency, and optimal performance.
Why Network Monitoring is Critical for Your NOC
Network monitoring activities are required for detection and resolution of issues—be it performance, security, or compliance—within IT infrastructure. Effectively, tracking network services has its maximized objectives as follows:
Prevent network outages: Ensure that your network as well as applications hosted on it remain perpetually accessible.
Obtain higher levels of performance: Identify the bottlenecks restricting the flows and processes and, in turn, improve the entire network’s efficiency.
Identify and react to security threats: Safeguard your infrastructure against cyber threats by identifying weaknesses early.
Ensure compliance: Help your business implement best practices by safeguarding important areas of your network.
The types of network monitoring your NOC offers will determine how well your network is managed, incidents are detected and resolved, and resource utilization. Let us review key network monitoring types every NOC should offer.
Monitoring Networks in Real Time
NOCs can perform a continual assessment of the condition of network devices, applications, and services with real-time monitoring. This monitoring type quickly helps remedy performance issues and failures by automating fixes.
Primary Areas for MR Time Monitoring:
Network traffic: Analyzing the transmission of data within the network for any possible congestion or bottlenecks.
System uptime: Ensuring critical services and systems are functioning and accessible to end-users.
Server health: Evaluating the performance and resource allocation of servers to avoid crashes.
Why It Matters:
There is no substitute for real-time network availability, and NOC teams are better able to prevent issues with the network downtimes. Reducing the time for maintenance dramatically increases productivity, and real-time oversight is pivotal for businesses with international reach or those that offer services depending on network availability.
Performance Monitoring.
A NOC is responsible for tracking all the operations that happen within the network. Network performance monitoring is of paramount significance in NOC operations since it ensures employees are performing optimally as it assists to monitor network speed, latency and performance indicators. Controlled network performance helps in detection of improvement areas in critical network areas such as bandwidth usage and congestion.
Key Areas for Performance Monitoring:
Bandwidth usage is critical for infection containment. It is essential to track all the applications and devices that are connected to the network to ensure they are not overusing bandwidth.
Network latency: High latency can have several negative impacts on application performance and result in many delays. Long distance routes seem to worsen the performance of applications, and measuring the time taken by data to travel from one point to another helps troubleshoot the problems.
Traffic patterns: Active understanding of the flow of traffic in and out of a network is helpful in managing resources for optimal performance and averting network congestion.
Why It Matters:
The performance monitoring feature enables your NOC to manage the network resource to the optimum which helps traffic to be controlled in an orderly manner and also boosts performance of applications and services. This is highly important for maintaining critical uptime and user experience in dynamic industries.
Security Monitoring
Network security monitoring enables detection and response to cyber threats, data breach, and other weaknesses that may breach the security of your network, as well as respond to them in a timely manner. Every NOC should have security monitoring 24/7 as part of a complete NOC so as to protect sensitive data and applications.
Key Areas for Security Monitoring:
Intrusion Detection and Prevention (IDS/IPS): Monitors the network and acts to mitigate traffic and other forms of attack associated with the network.
Firewall monitoring: Ensuring controlled access via firewalls is not breached by unauthorized users.
Threat detection: Employs methods to observe unhealthy behavior or traffic that is likely to signal an attack (DDoS, Phishing, Ransomware attacks).
Why It Matters:
Security monitoring helps to detect sensitive areas that can lead to cyber attacks and prevent such areas from being exploited. A robust security monitoring NOC will safeguard the network from breaches and threats.
Application Monitoring
Applications are foundational to many businesses. Ensuring performance management of applications is especially important in hosted services. Monitoring of the health of applications enables proactive action to be taken to avoid business productivity losses.
Key Areas for Application Monitoring:
Performance of business-critical applications: Monitoring the vitality, uptime, response metrics, and overall health of applications that are foundational to a business’s operations.
Database performance: Tracking the health of databases and the performance of the queries to avert lags that might cripple applications.
API performance: Checking the correct and active functioning of the APIs, especially for the cloud and SaaS based applications.
Why It Matters:
Monitoring applications helps in the prevention of service slowdowns, stagnation, and interruptions by detecting fault lines beforehand. This active surveillance for cloud hosted applications or for companies managing intricate applications guarantees the operations are streamlined. Businesses reap the benefits of improved operational efficiencies and user satisfaction.
Compliance Monitoring
These are monitored on specific industries that include healthcare, finance as well as government that focuses on protecting sensitive data and systems. These networks are tracked and documented for every action that influences compliance which helps maintain adherence to standards. Compliance monitoring guarantees sensitive data is safeguarded.
Important Areas for Compliance Monitoring:
Data encryption: Protecting sensitive data through encryption while being transmitted and stored for compliance with laws like HIPAA and GDPR.
Audit trails: Tracking and monitoring network activity logs to maintain a historical record of actions performed for the purposes of compliance verification.
Access controls: Maintenance of sensitive data and systems by ensuring that only authenticated users can access such information.
Why it Matters:
With compliance monitoring, your organization stands to gain from reduced legal and reputational risks, fines, and damage to reputation. Safeguarding your network from breaches as well as assuring a suspected compliance gap ensures regulatory compliance by avoiding the risk of non-compliance and fostering better trust appeal with clients and customers.
Cloud Monitoring
As more organizations adopt cloud infrastructure, cloud environments require monitoring as part of NOC services. Specialized tools for cloud monitoring enable NOCs to oversee the performance, security, and cost efficiency of their applications, cloud resources, and services.
Key Areas for Cloud Monitoring:
Resource usage: Allocation of specific resources (e.g., CPU, memory, storage) in cloud environments and their consumption is tracked for optimized cost and performance.
Cloud security: Cyber threats such as unauthorized access or data breaches calls for due diligence to mitigate those risks and ensuring security of the cloud environments.
Service uptime: Tracking availability as well as the uptime of hosted applications and services in the cloud.
Why it Matters:
The network operating center (NOC) teams need to track cloud services for performance, security, and cost-efficiency because the cloud environment is dynamic and constantly changing. Continuous cloud infrastructure monitoring makes certain that your cloud infrastructure is scalable, secure, and cost-effective.
Bandwidth and Traffic Analysis
Monitoring network traffic is as important as securing the network, so understanding it is equally important. NOCs are able to monitor bandwidth and analyze traffic to troubleshoot network problems like congestion and slowdowns, as well as ineffective utilization of resources.
Key Areas for Bandwidth and Traffic Analysis
Traffic flow: Establishing how the data moves through the network and adjusting routing to ease congestion and defeat bottlenecks.
Bandwidth usage: Keeping track of the total bandwidth consumption from different applications, devices, and users in relation to given performance benchmarks.
Traffic prioritization: Guaranteeing required bandwidth to high-priority applications for peak-performance, especially in hybrid and cloud-based settings.
Why it Matters:
Application and services’ availability relies heavily on proper allocation of monitored overhead resources, hence the need for comprehensive bandwidth allocation review alongside performance assessment to avert congestion.
Conclusion:
Organizations are now dealing with larger volumes of data and facing new competing traffic and security threats. This evolution has made network operations more challenging. To support efficient network operations, a Network Operations Center (NOC) needs to provide extensive multi-dimensional network monitoring across security, application performance, compliance, and cloud infrastructure.
With these automation tools, a NOC can manage the network proactively, ensuring optimal performance and availability while reducing security risks. A monitored network can guarantee business continuity, minimize downtime, improve security, and enhance user experience.
Every organization using a NOC requires their teams to deliver these critical functions to keep the network running smoothly and bolstered around the clock. Make sure your NOC team is prepared with all necessary tools to help achieve network stability and operational reliability.

